1. What is an API?
API, short for Application Programming Interface, is a set of rules and protocols that enables software applications to communicate and exchange data with each other. In simple terms, an API acts as a technical "contract": the requesting party knows exactly what information to provide, and the receiving party knows exactly what format to return results in.
In practice, when you book a flight on a travel website, the site does not store its own flight data. Instead, it calls the airline's API to retrieve real-time information. This is a classic example of how APIs operate in a modern enterprise environment.
APIs not only connect internal applications but also allow businesses to integrate third-party services into their systems, shortening development timelines and expanding capabilities without rebuilding from scratch.
2. What does an API consist of? Structure and core components
Endpoint
An endpoint is the specific URL that the client sends requests to. Each endpoint typically represents a defined resource or action within the system. For example, one endpoint may be used to retrieve a list of products, while another is used to create a new order.
Request and response
A request is the message the client sends to an API, including the HTTP method (GET, POST, PUT, DELETE), headers containing authentication details and data format information, and the body containing data to be transmitted when required.
A response is the reply the server returns after processing the request. Most modern APIs return data in JSON or XML format, along with an HTTP status code (200 means success, 401 means unauthenticated, 404 means resource not found, and so on).
Authentication
Authentication is the mechanism used to verify a client's identity before allowing access to an API. Common forms include API Keys (a secret string passed in the header), OAuth 2.0 (delegated access with limited scope), and JWT (JSON Web Token, which carries encrypted authentication information).
Rate limiting
Rate limiting is a mechanism that limits the number of requests a client can send to an API within a given time period. This protects the system from overload and prevents abusive behavior such as brute force attacks or unauthorized data scraping.
Documentation
Documentation is a complete reference describing how to use an API: the list of endpoints, methods, input parameters, response formats, and usage examples. Clear documentation helps developers integrate APIs more quickly and reduces the risk of misuse.
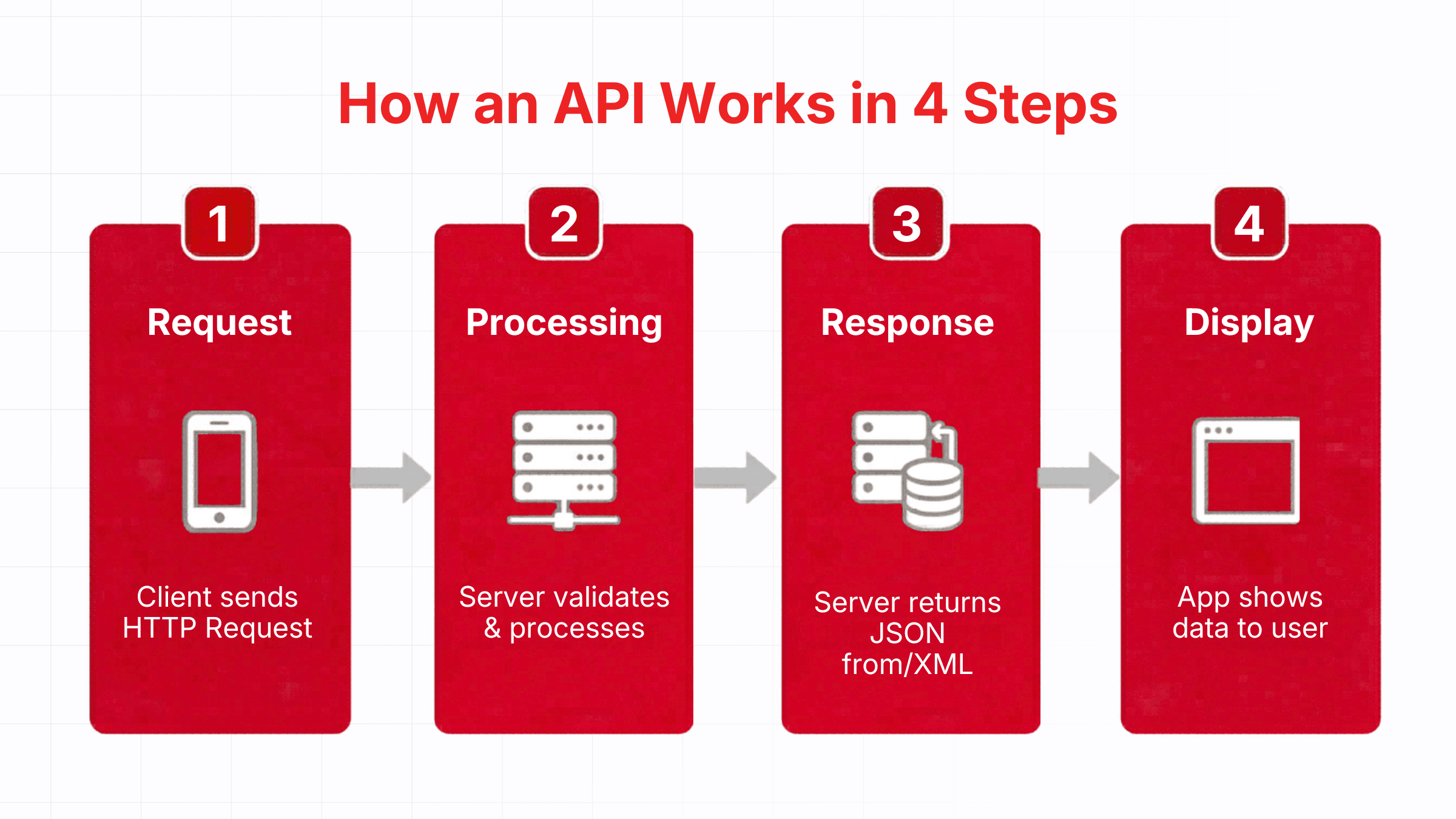
3. How an API works
An API operates through a closed-loop process consisting of four steps, which execute automatically within milliseconds each time a user makes a request.
- Step 1 - Send request: When a user performs an action in an app, such as pressing "Check today's weather", the client app sends an HTTP request to the server through an Endpoint. The request specifies the type of operation: GET to retrieve data, POST to submit, PUT to update, or DELETE to remove.
- Step 2 - Server processing: The server receives the request, authenticates the client's identity using an API Key or token, checks authorization, then executes the business logic, such as querying the database or calling additional internal services.
- Step 3 - Send response: The server packages the result and returns it in JSON or XML format along with an HTTP status code. Code 200 means success, 401 means unauthenticated, 404 means resource not found, and 500 indicates a server-side error.
- Step 4 - Display data: The client app receives the response, parses the data, and presents the information to the end user. In the weather app example, this is when the temperature and rain forecast appear on your phone screen.
4. Common API types today
There are several ways to classify APIs depending on the criteria used. The most common approach is by communication architecture, which yields three main types:
| API Type | Key characteristics | Advantages | Best suited for |
|---|---|---|---|
| REST API | Uses HTTP, returns JSON/XML, stateless | Simple, flexible, easy to integrate | Web apps, mobile apps, microservices |
| SOAP API | Standard XML protocol, strict schema | High security, supports complex transactions | Finance, banking, legacy systems |
| GraphQL API | Client specifies the exact data needed | Reduces over-fetching, flexible querying | Complex apps, real-time dashboards |
Beyond these three, gRPC is a protocol developed by Google that uses Protocol Buffers instead of JSON, making it well suited for communication between microservices that require high performance and low latency.
5. How to call an API and connect APIs for applications
What is an API call?
Calling an API is the act of an application (client) sending a request to an API endpoint to retrieve or send data. Each API call requires providing the correct HTTP method, the correct header structure, and the correct body format as specified by the API provider.
Basic steps for connecting to an API
- Read the API documentation to understand the endpoints, methods, and required parameters.
- Obtain authentication credentials: an API Key, OAuth token, or client credentials depending on the API type.
- Send a test request in a sandbox environment before moving to production.
- Handle the response: check the status code, parse the JSON or XML data, and manage errors.
- Implement a retry mechanism for temporary errors (429 Too Many Requests, 503 Service Unavailable).
When connecting APIs in a production application, businesses should pay attention to managing API Key lifecycles, setting appropriate timeouts, and maintaining comprehensive logs to detect anomalies in a timely manner. This is especially important when the system relies on multiple APIs running in parallel.
6. Free APIs and key considerations when using them
Free APIs are APIs that are offered at no cost or include a free tier with limits on the number of requests or available features. They are a popular choice for individual developers, early-stage startups, and businesses looking to test integrations before committing to investment. Common categories of free APIs used in practice include geographic and mapping data APIs, weather APIs, foreign exchange rate APIs, postal code lookup APIs, and shipping information APIs. Many cloud computing platforms also provide free-tier APIs for resource management, storage, and user authentication.
Despite their convenience, free APIs come with risks that businesses need to be aware of:
- API Keys can be exposed if embedded in source code or deployed in unsecured environments.
- Data transmitted through third-party APIs may be logged if not properly encrypted.
- Free tiers typically do not guarantee SLA uptime, which can lead to unexpected service interruptions.
- Usage policies may change at any time, affecting systems that depend on the API.
7. API security risks and how to mitigate them
Design and configuration flaws
Poorly designed or misconfigured APIs are the leading cause of security incidents. Common issues include incorrect access controls (allowing users to access other people's data), missing input validation, and exposing system information in error messages.
Mitigation: design APIs using the principle of least privilege (grant only the minimum permissions required), validate input schemas thoroughly before processing, and suppress stack traces from error responses.
Injection attacks via API
SQL injection and XSS are the two most common injection attack types targeting APIs. Attackers inject malicious code into request parameters, exploiting APIs that do not validate input to execute unauthorized commands or steal data from the database.
Mitigation: deploy a WAF (Web Application Firewall) capable of analyzing API traffic, validate and sanitize all input data, and use parameterized queries instead of direct string concatenation.
Brute force attacks and authentication abuse
Attackers can use brute force to guess API Keys, passwords, or authentication tokens. When successful, they gain full system access as if they were a legitimate user.
Mitigation: combine strict rate limiting, account lockout after multiple failed authentication attempts, multi-factor authentication for sensitive APIs, and periodic API Key rotation.
Data breach via uncontrolled APIs
Shadow APIs (forgotten or no-longer-used APIs that remain active) are a serious risk. These APIs typically lack security patches, have no monitoring, and become easy entry points for attacks that lead to a data breach.
Mitigation: maintain a complete inventory of all active APIs, decommission outdated ones, and set up alerts when anomalous endpoints are detected in the system.
DDoS attacks targeting APIs
A DDoS attack against an API at Layer 7 is often difficult to detect because the requests appear completely legitimate. Attackers send large volumes of requests to resource-intensive endpoints to exhaust the server's processing capacity.
Mitigation: deploy WAAP (Web Application and API Protection) with the ability to distinguish between legitimate traffic and automated attacks, combined with auto-scaling and CDN to distribute load.
8. VNIS - VNETWORK's comprehensive Web/App/API security solution
VNETWORK developed VNIS (VNETWORK Internet Security), a Web/App/API security platform designed to protect businesses against all the API attack vectors described above. VNIS integrates multiple layers of protection within a unified system, allowing technical teams to manage security centrally rather than patching individual vulnerabilities one by one.
VNIS API security features:
- AI WAF integration: Detects and blocks injection attacks, XSS, CSRF, and threats from the OWASP Top 10 in real time at the application layer.
- Intelligent API rate limiting: Controls API traffic per client, endpoint, and usage behavior, preventing abuse without disrupting legitimate users.
- Layer 7 DDoS protection: Filters attack traffic targeting APIs without interrupting normal system operations.
- Access control: Granular authentication and authorization that allows businesses to precisely control which clients can call which endpoints.
- 24/7 SOC: A dedicated cybersecurity team providing continuous monitoring, early detection of anomalous behavior, and timely incident response.
9. Conclusion
APIs have become an indispensable component of modern software architecture. Understanding what an API is, what it consists of, and how to call APIs correctly is the foundation that allows businesses to build flexible and efficient connected systems. However, with those benefits comes the serious responsibility of securing APIs against increasingly sophisticated threats.
Businesses cannot afford to let APIs operate without a dedicated protection layer. VNETWORK is ready to partner with you through the VNIS solution, covering the entire attack surface from Web and App to API. Contact us now via hotline +84 (028) 7306 8789 or visit vnetwork.vn for a free consultation.
FAQ - Frequently asked questions about APIs
1. What is an API in the simplest terms?
An API (Application Programming Interface) is an interface that allows two software applications to communicate with each other. Think of an API like a waiter at a restaurant: the customer (client) places an order, the waiter relays the request to the kitchen (server), then brings the result back. APIs play that same role in the world of software, defining the format of requests and how results are returned between systems.
2. What does an API consist of technically?
An API typically consists of these core components: an endpoint (the URL that receives requests), HTTP methods (GET, POST, PUT, DELETE), headers (authentication details and metadata), a request body (data to be sent), a response (data returned in JSON or XML), an authentication mechanism, and documentation describing how to use it.
3. What is an API call and how do you connect to an API?
Calling an API is the act of sending a request from your application to an API endpoint to retrieve or write data. To connect to an API, you need to: read the provider's documentation, obtain authentication credentials (API Key or OAuth token), send a test request in a test environment, then handle the response data in your application code.
4. Are free APIs safe to use in real projects?
Free APIs can be used but require caution. The main risks include: API Keys being exposed if not managed carefully, lack of guaranteed uptime and SLA, and usage policies that can change at any time. For production projects, you should carefully review the terms of service, encrypt all data transmitted through the API, and never embed an API Key directly in source code.
5. How can businesses secure their APIs?
Businesses need to combine multiple layers of protection: strong authentication (OAuth 2.0, JWT), rate limiting to prevent abuse, a WAF capable of analyzing API traffic, encryption of transmitted data, and regular audits of all active APIs. VNETWORK's VNIS solution provides all of these layers in a unified platform, combining AI for new threat detection and a 24/7 SOC team for incident response.